Switch content of the page by the Role togglethe content would be changed according to the role
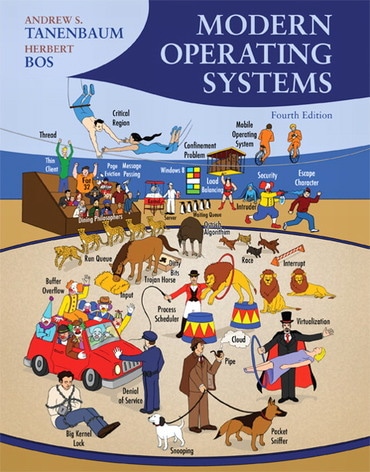
Modern Operating Systems, 4th edition
Published by Pearson (March 10, 2014) © 2015
- Andrew S. Tanenbaum rije University, Amsterdam, The Netherlands
- Herbert Bos
Hardcover
$197.32
Price Reduced From: $246.65
ISBN-13: 9780133591620
Modern Operating Systems
Published 2014
Need help? Get in touch